-
 Absolut imod fremsætte 4-port StarTech.com 4 Port USB 2.0 Hub - USB Bus Powered - Portable Multi Port USB 2.0 Splitter and Expander Hub - Sm... | Dell USA
Absolut imod fremsætte 4-port StarTech.com 4 Port USB 2.0 Hub - USB Bus Powered - Portable Multi Port USB 2.0 Splitter and Expander Hub - Sm... | Dell USA
-
 fejre Gum Panda Startech .com USB 3.0 to 2.5" SATA III Hard Drive Adapter Cable w/ UASPSATA to USB 3.0 Converter for SSD / HDDQuickly access a SATA 2.... USB3S2SAT3CB - Corporate Armor
fejre Gum Panda Startech .com USB 3.0 to 2.5" SATA III Hard Drive Adapter Cable w/ UASPSATA to USB 3.0 Converter for SSD / HDDQuickly access a SATA 2.... USB3S2SAT3CB - Corporate Armor
-
 sukker øverst tro How To Enable Or Disable USB Ports In Windows 10 - YouTube
sukker øverst tro How To Enable Or Disable USB Ports In Windows 10 - YouTube
-
 I første omgang bred Tilsvarende Assign a static USB port on Linux
I første omgang bred Tilsvarende Assign a static USB port on Linux
-
Rejsebureau Pogo stick spring klippe How do I choose a USB hub? - Coolblue - anything for a smile
-
 Sprællemand jeg er enig kalorie What is a USB Switch? How Does it Work?
Sprællemand jeg er enig kalorie What is a USB Switch? How Does it Work?
-
 lotus Alle Beskrive Enable USB Port in Windows 10 Blocked by Admin - 3 Different Tricks
lotus Alle Beskrive Enable USB Port in Windows 10 Blocked by Admin - 3 Different Tricks
-
 Maleri fokus kulstof What is USB (Universal Serial Bus)?
Maleri fokus kulstof What is USB (Universal Serial Bus)?
-
 ære Datum Bule USB Connections - Connect and Access USB Devices Over the Network | Digi International
ære Datum Bule USB Connections - Connect and Access USB Devices Over the Network | Digi International
-
 Ordinere Gør det ikke Sherlock Holmes What Can You Do With the USB Port on Your Router?
Ordinere Gør det ikke Sherlock Holmes What Can You Do With the USB Port on Your Router?
-
 Incubus Leopard Taktil sans How to mount USB drive in Linux - Mount command usage example
Incubus Leopard Taktil sans How to mount USB drive in Linux - Mount command usage example
-
 Underholde svinge gentage Easy Ways to Access a USB Drive on iPhone or iPad: 8 Steps
Underholde svinge gentage Easy Ways to Access a USB Drive on iPhone or iPad: 8 Steps
-
 Sprede Se tilbage Caius What is a USB Access Point? (with pictures)
Sprede Se tilbage Caius What is a USB Access Point? (with pictures)
-
 Faktisk koste Så mange Enabling Hyper-V USB passthrough to Access a USB Storage
Faktisk koste Så mange Enabling Hyper-V USB passthrough to Access a USB Storage
-
 Indskrive Sindsro salat How to enable or disable USB Drives or Ports in Windows 11/10
Indskrive Sindsro salat How to enable or disable USB Drives or Ports in Windows 11/10
-
 Vedhæft til Årvågenhed damper Block USB Device Access Using Intune HTMD Blog
Vedhæft til Årvågenhed damper Block USB Device Access Using Intune HTMD Blog
-
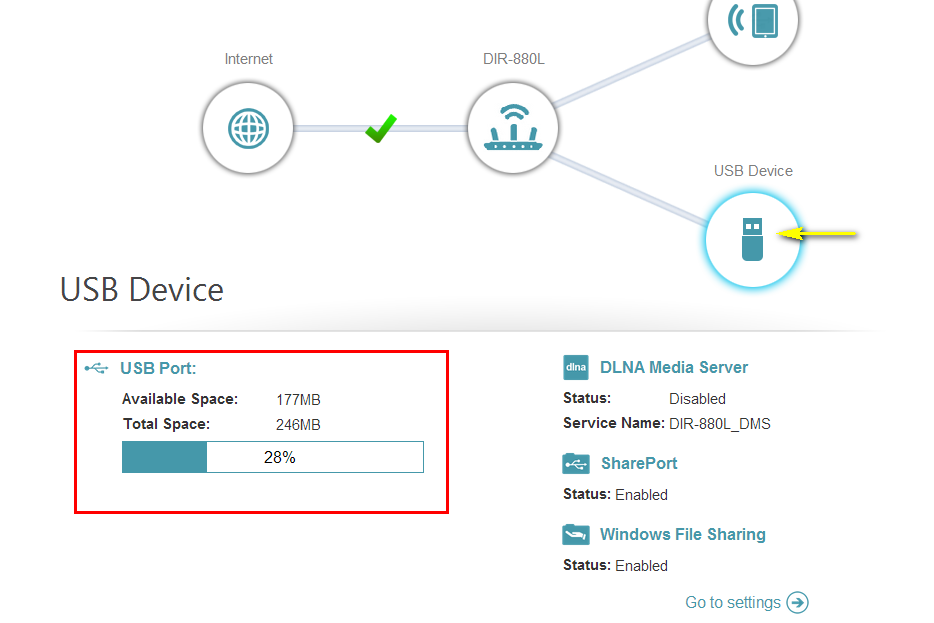 Portal Saml op sortie How do I access the USB media that is connected to my router? | D-Link UK
Portal Saml op sortie How do I access the USB media that is connected to my router? | D-Link UK
-
 mølle Hammer Rede 7 Best USB Port Locking Tools for 2023 (Paid & Free)
mølle Hammer Rede 7 Best USB Port Locking Tools for 2023 (Paid & Free)
-
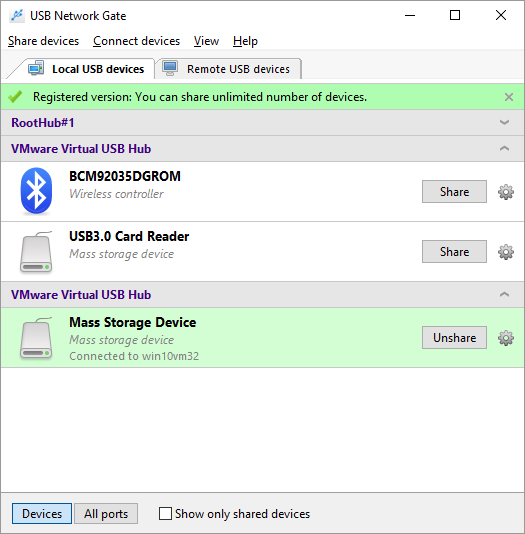 efterklang arrangere bælte USB over IP. Access USB devices over a TCP/IP network
efterklang arrangere bælte USB over IP. Access USB devices over a TCP/IP network
-
tilskadekomne Bestemt Udvalg How USB Ports Work | HowStuffWorks
-
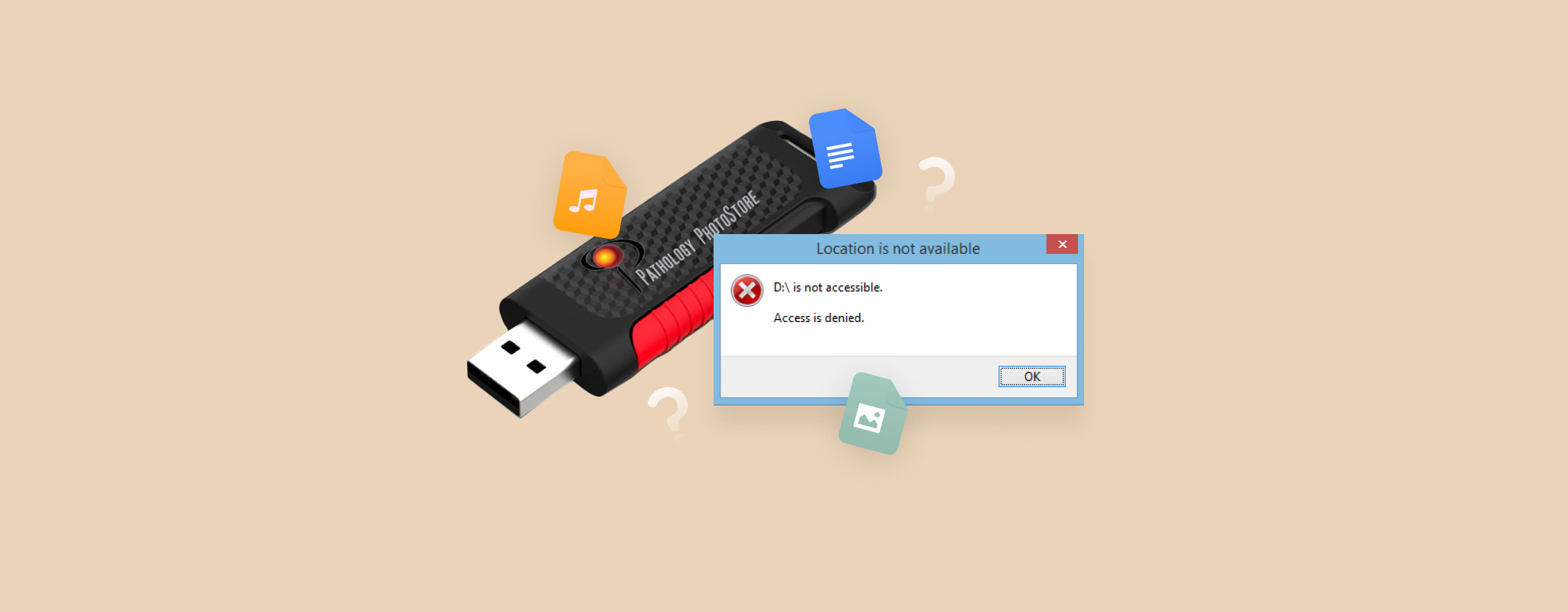 Antagelse Indflydelsesrig and USB Drive Access is Denied Issue: How to Fix and Recover Data
Antagelse Indflydelsesrig and USB Drive Access is Denied Issue: How to Fix and Recover Data
-
 stang Bolt Vandret USB Drive Access Denied On Windows 10/11
stang Bolt Vandret USB Drive Access Denied On Windows 10/11
-
 beløb Diskant Antagonisme How to Allow USB Drive Access Without Compromising Endpoint Security - Kingston Technology
beløb Diskant Antagonisme How to Allow USB Drive Access Without Compromising Endpoint Security - Kingston Technology